A developer identified an attack in his dev virtual machine running on datacenter, and also he found an HTML file named READ_TO_DECRYPT in his desktop
Read Protect or Ship Bitcoin or lose data – Ransomware attack
After reading that HTML file, the user understood its a ransomware, all his files were encrypted with strong AES-256 Algorithm. and also it was mentioned to pay bitcoin of 0.145 to the mentioned wallet and to contact the onion email id with the Identification to get the decrypt key.
The current value of the demanded BTC is almost 73K in Indian Rupee

A Brief about their Infrastructure
The confidential client is running his small datacenter in 3rd party environment, he runs ESXi 6.5 on his datacenter and managed through vCenter, He has a 100TBs size storage server connected to the ESXi as datastore through MultiPath iSCSI.
All the developers have a thin client to connect to their VM in the datacenter to work, and fortunately, they have deployed Nimesa for POC very recently. I helped in setting up the Nimesa in their datacenter, added vCenter and Storage, configured 4 backup groups with different level of backups. The affected systems are in one backup group and all having hourly backup enabled
How I recovered the Virtual machines
The first thing we did is we stopped the backups because as it is a developer machine they have configured the very few backup retentions we don’t want to delete the good copy of backups by the retention.

And we also noted, the recent successful backups are at 13:00 and 14:00th hour of the day, we best case we will have 18 mins of data loss and worst 1 hour of data loss even if the last backup is not good.
System status
The system is up and running, user can connect to the system through RDP, only the user files are encrypted and none of the OS files got affected.
Unfortunately, the NAS target connected with other backup software was mounted on the system, those backup files were also encrypted.
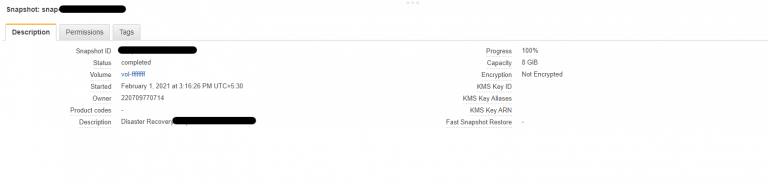
Nimesa leverages storage snapshots for backups which are immutable, so any malware cannot infect the storage snapshots.



Restore Operation
Then, we deleted the virtual machine from the vCenter and initiated restore from the recent safe backup. Within 5 minutes, the user got the virtual machine in the same state where he left.

Instead of paying the ransom to hackers, they recovered all the virtual machines through Nimesa instantaneously.
Virtual Machines are renamed for the video recording purpose.
Also published on Medium.