Data Protection (Backup and DR) describes the process of creating and storing the data that can be used to recover against data loss
A proper backup copy is stored in a separate system or medium, such as tape, from the primary data to protect against the possibility of data loss due to primary hardware or software failure. Read more about 3-2-1 Backup strategy here
Why Data Protection so important
The purpose of the backup is to create a copy of data that can be recovered in the event of a primary data failure. Primary data failures can be the result of hardware or software failure, data corruption, or a human-caused event, such as a malicious attack (virus or malware including Ransomware), or accidental deletion of data.
Backup copies allow data to be restored from an earlier point in time to help the business recover from an unplanned event.
Things to consider before approving the backup strategy
How is it backed up?
A High-quality backup will protect you from accidental deletion, ransomware malware, hardware failure, power outages, and other catastrophic events.
If your backup is always full, you will end up paying more for the backup media cost, and also the time to backup will also increase which result in bad RPOs
If you are creating a more incremental backup and very less periodic full backup then the time to restore will be high as the backup system will restore the full backup and apply all the incremental backups one by one to achieve the restore this will result in bad RTOs
Are your backups consistent, is the application running on the system flushes all the buffer to disk? all the transactions are fully committed? Any dirty buffer is there while backup? these can make the backup non-restorable. You can keep the backup for compliance, not for the restoration purpose. Read more about the backup types
Where it is been stored?
After you know how the backup has been taken, you should consider where the backups are stored, Are you storing the backup in the same system?
Assume you take the backup of your mobile and stored in the same mobile. you can restore only when some of the files are deleted but not recover when the storage is corrupted, lost phone scenarios like there
Where you store the backup is also very important, Sometimes we take backup and keep it same disk or same system or same location
To support the recovery on disaster, you should think of same storage system, near DR site, Far DR Site
Read more about the 3-2-1 Stragety.
What data does my backup have?
You should understand the organization’s data landscape, what is stored in databases, what is stored in files, where it is stored, what is the data change rate
If you are using multi-tier application deployed on multiple nodes, the backup policy should be backing up the nodes all at same time or depends on your architecture
For some applications, there is no need to back up the application server only the database backup is enough, For some architecture, the application server, database server, media server all need to backup at the same time. So you should understand the landscape clearly where the records or information is stored
Who has the access to your backups?
Ransomware malware is becoming more intelligent, it targets the backup first and makes your backups non-recoverable. so who has the access to the backup storage is also important.
Assume you have storage media attached to the system through NAS protocol, ransomware malware can encrypt the files in your backup media also.
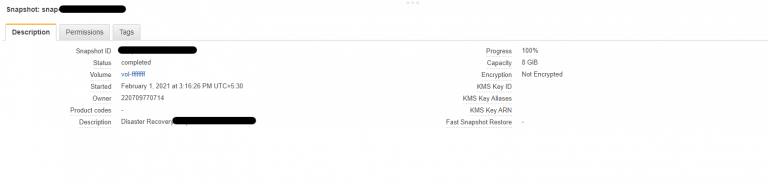
In another case, you keep all your snapshots of your Cloud volumes in the same account and the developer has the write access to it, and he configured the keys to the CLI installed on his laptop and his laptop got infected, the malware can run a script which deletes all the snapshots on his account which causes you will have no recovery points, So keeping a vault account and securing the access to the backup account/storage is very important
Also published on Medium.